New 250GB Plans LIVE now.


Share Video Privately Securely with Your Team
Opting to share video privately is about much more than just hiding a URL. True private sharing relies on dedicated tools built with robust security—think password protection, granular access controls, and encryption—to guarantee your content is only seen by the people you've chosen.
Why Unlisted Links Aren't Truly Private
That 'unlisted' button on a public video platform can feel reassuring, but in reality, it’s a bit like hiding your house key under the doormat. It provides a flimsy layer of obscurity, not real security. Anyone who gets their hands on that link can watch your video and, more importantly, share it with others. For creative agencies or corporate teams handling sensitive projects, this is a massive risk.

The Real-World Risks of Hidden URLs
Picture this: your agency sends a client the 'unlisted' link for a major pre-launch campaign video. The client, with the best intentions, forwards it to another department for a quick look. Just like that, your confidential asset is out in the wild, circulating uncontrollably before the big reveal. Since the link itself is the only key, you have no way to revoke access or even track who has seen it.
This lack of control isn't the only problem. These links can easily get exposed—popping up in browser histories, getting accidentally pasted into a public Slack channel, or even being scraped by bots. Once the link is out, the cat is out of the bag for good.
Platform Policies and Ownership Concerns
Beyond the risk of accidental leaks, the terms of service on public platforms can be a real headache. When you upload your video, you often grant the platform a sweeping license to use your content. While they probably won't feature your unlisted corporate training video on their homepage, your intellectual property is still subject to their rules, which might not line up with your company’s security and compliance requirements.
An unlisted link is a shareable secret. A private link is a locked door that only opens for specific people you've approved. This distinction is critical for professional workflows where intellectual property and confidentiality are paramount.
To bring this into focus, let's compare the two approaches side-by-side.
Public Unlisted vs True Private Sharing A Quick Comparison
The table below breaks down the fundamental differences between hiding a video on a public site versus using a purpose-built private sharing tool.
Feature | Public Platform (Unlisted) | Dedicated Private Solution |
|---|---|---|
Access Control | Anyone with the link can view and share it. | Restricted to specific, authenticated users (e.g., by email address). |
Security | None. Relies solely on the link remaining secret. | Multi-layered: passwords, SSO, watermarking, encryption, link expiration. |
Revoking Access | Impossible without deleting the video and creating a new one. | Simple. Access can be revoked for individual users or groups instantly. |
Audit Trails | Limited or non-existent. You can't see who viewed it. | Detailed logs show who viewed the content, when, and for how long. |
Content Ownership | Governed by the platform's broad terms of service. | You retain full ownership and control over your intellectual property. |
Branding | Hosted on a public domain with the platform’s branding. | Hosted on a secure, often brandable portal, maintaining a professional appearance. |
As you can see, the gap is significant. For any serious professional work, relying on an unlisted link is a gamble.
The increasing demand for more secure methods has fueled serious market expansion. The global private video hosting platforms market is growing as more businesses realize they need to share video content without public exposure. This trend shows a wider understanding that professional needs have simply outgrown basic unlisted options. You can explore more data on the private video hosting market to see just how this sector is evolving.
Ultimately, to properly share video privately, you need tools built for security from the ground up. It’s time to move away from hidden URLs and embrace solutions that give you true access control, audit trails, and encryption. It's about making sure your hard work—your intellectual property—remains yours and is only seen by the eyes you intend.
Locking Down Your Videos: A Practical Guide to Access Control
When you share video privately, true security isn’t about a single lock; it's about having the right set of keys and knowing exactly who holds them. You need to be in complete control. This means moving past simple "unlisted" links and adopting layers of protection that you can tailor to any project, client, or internal team.
The first and most essential layer is password protection. It’s the digital deadbolt for your video. A simple link can be forwarded, clicked, and viewed by anyone who gets their hands on it. But a password-protected link requires a key, immediately creating a barrier to entry.
The Everyday Essentials: Passwords and Expiration Dates
Let’s get practical. Imagine you've just wrapped up a first cut for a client on a Friday afternoon. You need their feedback over the weekend, but you definitely don't want that link floating around the internet forever. This is the perfect use case for combining a password with an expiring link.
You can set that review link to simply stop working on Monday morning. This does two things brilliantly: it creates a clear, finite window for feedback and it prevents that specific version from being accessed or shared long after its purpose is served. It's a simple, powerful way to maintain control.
These features are the bedrock of any secure collaboration workflow. A dedicated video review platform like PlayPause builds these controls right in, giving you the tools to manage access from the second you hit "share."
Pro-tip: Think of expiring links as a project management tool, not just a security feature. They create a natural sense of urgency, nudging stakeholders to provide timely feedback and preventing old, outdated versions of a video from causing confusion later on.
With video now central to so many business functions—a massive 89% of businesses now use it for marketing—these controls are non-negotiable. As companies rely on secure platforms to share targeted content, 95% of video marketers see it as a vital part of their strategy. If you're curious, you can dig into more video marketing trends to see just how big this shift is.
Advanced Protection for High-Stakes Content
For projects that are highly sensitive, you need to bring in the heavy artillery. Basic passwords won't cut it when you're dealing with a pre-release film, a confidential corporate announcement, or valuable intellectual property.
One of the most effective advanced controls is domain whitelisting (sometimes called domain restriction). This feature lets you dictate where your video can be played. For example, you can lock an internal training video so it will only play when embedded on your company’s intranet. If someone tries to copy the embed code and post it on a public blog or social media, the player simply won't load.
Another incredibly powerful tool is dynamic watermarking. This is not your typical faint logo in the corner. Instead, the platform overlays viewer-specific information—like their email address, IP, or the time they're watching—directly onto the video as it plays.
This is a massive deterrent. If someone decides to screen-record the video to leak it, their personal details are burned right into the footage. It makes the source of a leak instantly traceable, which makes people think twice. The image below shows a static watermark, but imagine this text being personalized for every single viewer.
These advanced features are critical for situations like:
Pre-release film screeners: Send cuts to festival judges or critics with their name clearly visible on the footage.
Confidential corporate announcements: Keep internal messages under wraps before they go public.
High-value training courses: Protect your IP from being stolen and resold.
By layering these robust controls, you create a secure viewing environment that you can adjust based on how sensitive the content is. You're no longer just deciding who can watch, but also where and how, giving you total peace of mind.
Making Your Creative Review and Approval Workflow Bulletproof
When you share video privately, you're doing more than just stopping leaks. You’re building a smarter, faster, and far less chaotic way for your team to collaborate. We've all been trapped in those endless email chains with vague feedback like, "can you fix that part around 30 seconds in?" It's a surefire recipe for confusion, missed notes, and wasted hours on unnecessary re-renders.
A truly effective workflow takes feedback from a frustrating guessing game and turns it into a clear, actionable to-do list. The secret is to pull the entire conversation out of scattered inboxes and anchor it directly to the video timeline. This creates a single source of truth that everyone can rely on.
This flow chart below shows how different security layers—like passwords, link expirations, and watermarks—can work together to form a solid foundation for secure sharing.
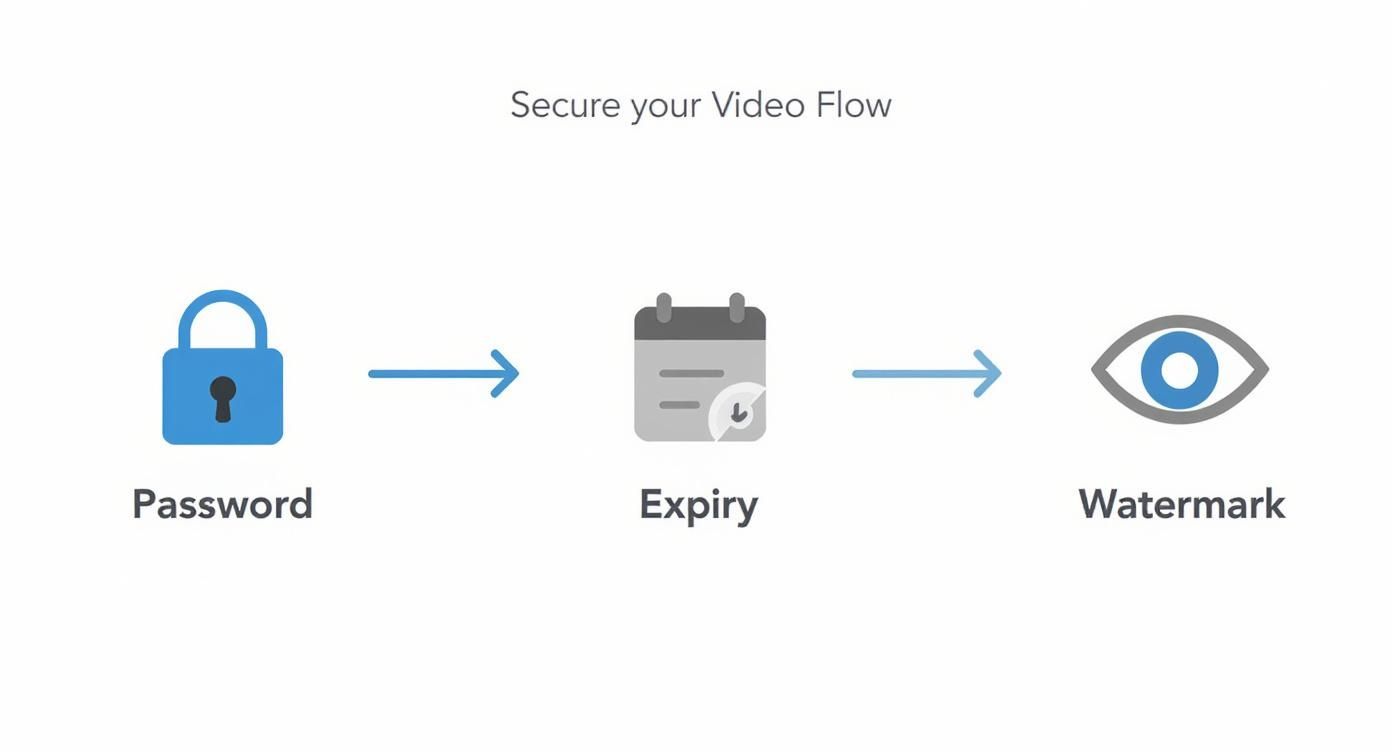
As you can see, layering your security measures ensures that even if a link gets forwarded, access stays controlled and traceable.
Establishing Clear Roles and Permissions
A smooth review process starts with making sure everyone has just the right amount of access. One of the most common missteps is giving everyone "editor" permissions, which is a fast track to accidental approvals or a flood of conflicting feedback. A more granular permission model brings much-needed order to the chaos.
Just think about the different people involved in your projects:
Viewers: Perfect for executives or stakeholders who only need to see the latest cut. They can watch the video but can't comment or approve versions, which keeps the feedback channel clean and focused.
Commenters: This is your core creative team—the directors, copywriters, and project managers. They need to leave time-coded comments and reply to threads, but they don't have the final say.
Approvers: These are the key decision-makers, usually the client or an executive producer. They hold the power to mark a version as "Approved," which locks it down and signals that the work is officially done.
Assigning roles like these creates a clear hierarchy for feedback. You’ll know instantly whose notes are suggestions and whose word is the final one.
To help visualize this, here’s a quick breakdown of how these roles typically function in a collaborative video review platform.
Permission Roles for Collaborative Video Review
Role | Viewing Permissions | Commenting Access | Downloading Rights | Approval Power |
|---|---|---|---|---|
Viewer | Can view all shared versions | None | Usually disabled by default | None |
Commenter | Can view and switch between versions | Can add new comments and reply to threads | Can be enabled/disabled as needed | None |
Approver | Full viewing and version access | Full commenting and reply access | Typically enabled | Can mark versions as "Approved" or "Needs Changes" |
By setting up a clear structure like this from the start, you eliminate confusion and ensure that feedback flows through the proper channels, making the entire process more efficient.
Transforming Feedback with Frame-Accurate Comments
The real magic happens when feedback is visually tied to the exact moment it refers to. Modern review platforms let stakeholders click on a specific frame and drop a comment that’s time-stamped down to the millisecond. This simple feature completely wipes out ambiguity.
A vague note like, "The logo animation feels a bit slow," becomes a concrete, actionable comment at 00:00:12:03 that says, "Can we speed up the logo resolve by about 15% right here?" That’s a note an editor can execute immediately, no questions asked.
A great private sharing platform turns every single piece of feedback into a trackable task. Once a comment is addressed, it gets checked off the list, creating a transparent record of every change request and its status.
Many tools go even further, offering on-screen drawing and annotation. A client can circle a distracting element in the background or draw an arrow pointing to a color that feels off. This visual context is invaluable and drastically cuts down the back-and-forth, saving everyone hours of frustration. For more tips on optimizing your team's workflow, feel free to check out the PlayPause blog.
Mastering Version Control Without the Mess
We’ve all seen it: project folders littered with files named Final_v2, Final_v3_ClientNotes, and the dreaded FINAL_FINAL_ThisOne. This is a classic symptom of a broken workflow. A proper review system handles versioning for you, automatically stacking new uploads on top of old ones in a single, easy-to-follow timeline.
When a stakeholder opens a review link, they always see the latest version first. But with a single click, they can jump back to previous versions to compare changes side-by-side. This is incredibly useful for confirming a note was addressed correctly or even for revisiting an earlier creative decision.
This version stacking feature is a game-changer for two key reasons:
It Reduces Confusion: No one is ever accidentally reviewing and leaving notes on an old, outdated cut.
It Creates a Record: You get a complete, auditable history of the project's entire evolution, from the first rough assembly to the final approved master.
By putting these structures in place—clear roles, frame-accurate feedback, and organized versioning—you’re doing so much more than just sharing a video privately. You're creating a controlled, efficient, and truly collaborative space where your team's energy is spent on the creative work itself, not on deciphering confusing emails or hunting for the right file.
Making Your Private Sharing Platform Talk to Your Other Tools
A video sharing platform that doesn't connect with your other software is more of a roadblock than a solution. If it’s living on its own little island, you're stuck in a cycle of downloading, re-uploading, and manually notifying people. That’s not just annoying—it’s a time sink and a recipe for mistakes.
The real magic happens when your sharing platform becomes a central hub that speaks the same language as your editing software, your project management tools, and your team's chat app. When everything is connected, you build a smooth, automated workflow that frees up your team from tedious busywork.
Connect Directly to Your Editing Timeline
One of the biggest game-changers is integrating your video platform directly with your Non-Linear Editor (NLE). Think about your current process. You finish a cut in Adobe Premiere Pro or After Effects, then you have to export, compress, and upload it. It's a clunky, multi-step process.
With a direct NLE integration, you can install a panel right inside your editor. When a new version is ready, you just click a button to send it straight to the review platform. No more exporting and uploading. This creates a frictionless path from your creative timeline to your client’s inbox, which means you can share updates more often and get feedback faster.
Get Real-Time Notifications Where Your Team Actually Works
Let's be honest, no one wants to live in their email inbox waiting for feedback notifications. Modern teams live in apps like Slack or Microsoft Teams. That's where you need your updates to appear.
By setting up these integrations, you can get instant alerts for the stuff that actually matters:
A client just dropped a new comment on the V3 cut.
The producer marked the final version as "Approved."
A new freelancer was just added to the project space.
This keeps your project manager in the loop without them having to constantly check another website. It closes the gap between a client leaving a note and your editor jumping on the revision, keeping the project's momentum going.
When you hook your video review platform into your chat tools, you turn static notifications into active conversations. A simple Slack alert can start a discussion right then and there, letting your team make decisions on the fly.
Simplify Access and Boost Security with Single Sign-On
For any studio or agency with more than a handful of people, managing dozens of separate logins is a nightmare for both IT and your team. This is where Single Sign-On (SSO) comes in. SSO lets everyone log into your video platform using the credentials they already have, like their company Google or Microsoft account.
This diagram shows how SSO works—it uses a central, trusted service to verify a user's identity before granting them access to other connected apps.
The real-world benefit is twofold:
Tighter Security: Access is managed from one central place. When someone leaves the company, IT just disables their main account, and their access to the video platform is cut off instantly. No more hunting for rogue accounts.
Less Hassle for Users: Your team doesn't need to create and remember yet another password. They just log in once and get secure access, which means fewer "I forgot my password" tickets for you to deal with.
Build Custom Automations with APIs
If you really want to dial in your workflow, you can use an Application Programming Interface (API) to create custom connections between your tools. This is definitely more technical, but the potential is massive for eliminating manual steps.
For example, you could set up an automation where marking a task as "Ready for Review" in Asana or Jira automatically triggers a sequence of events:
A new, secure review link is generated in your video platform.
The right people—say, the client and the creative director—are automatically invited.
The new link is posted directly into the project's Slack channel.
This kind of setup removes the human element from handoffs entirely, ensuring the review cycle starts the moment an edit is finalized. If you're looking to build out a custom workflow like this, diving into a platform's API documentation is the first step. For more tailored help, you can always contact a specialist team for advice on designing a system that works for you.
Meeting Compliance and Data Security Standards
For a lot of industries, sharing video privately isn't just about protecting your work—it's a serious legal and regulatory minefield. If you're in healthcare, finance, or the legal field, a single leak goes way beyond embarrassment. It can lead to massive fines and completely shatter the trust you've built with your clients. This is where you need more than just basic security; you need serious governance features.
Getting this right means leaving simple passwords in the rearview mirror and adopting tools built from the ground up for accountability and control.
The Unblinking Eye of Audit Trails
Let's play out a scenario. You've shared a sensitive deposition video with a legal team. A few days later, a key clip mysteriously appears online. How do you trace the source? Without a proper audit trail, it’s a guessing game. An audit trail eliminates the guesswork by creating a detailed, unchangeable record of every single interaction with your video file.
Think of it as your video's definitive history book. It logs every critical data point:
Who accessed the file, tied directly to their authenticated user account.
When they watched it, complete with precise timestamps for every view.
What they did, tracking every play, pause, comment, and download attempt.
This isn't just nice to have; it's essential for any workflow where compliance is a factor. It gives you the hard evidence you need for internal investigations and proves to regulators that you have a secure, traceable process locked down.
Navigating Data Residency and Regional Laws
In a global workflow, where your data lives is just as critical as how it's protected. Regulations like GDPR in Europe or CCPA in California have incredibly strict rules about where their citizens' data can be stored. If your company operates internationally, you can't just park European client videos on U.S. servers and call it a day—not without navigating a complex web of legal requirements.
This is exactly why data residency options are a non-negotiable feature. You need a platform that lets you choose the geographic region for your media storage. For instance, you could select a server cluster in Frankfurt specifically for your EU clients. This ensures you're respecting local data sovereignty laws and avoiding the kind of legal trouble and hefty fines that can derail a project.
Keeping data within a specific jurisdiction isn't just a technical detail; it's a core component of a modern global security strategy. It’s how you show clients you take their regional data privacy rights seriously.
Shielding Your Content with End-to-End Encryption
Finally, let’s talk about the ultimate shield for your intellectual property: robust encryption. Real security means protecting your files at every single point in their lifecycle. This is what we call end-to-end encryption.
It works by securing your video in two critical states:
In Transit: As your file is being uploaded or streamed, it's vulnerable to interception. This encryption protects it from man-in-the-middle attacks while it's traveling across the internet.
At Rest: Once your file is sitting on a server, this encryption scrambles the data, making it completely unreadable to anyone who might gain unauthorized access to the physical hardware.
The demand for this level of security is skyrocketing. The market for controlled content delivery is growing fast, with live streaming alone projected to reach $345 billion by 2030. Much of that growth is driven by private broadcasts—businesses using secure platforms for confidential town halls, training, and events. This just highlights how critical these security layers are. You can find out more about these live streaming statistics to see the full picture.
By combining airtight audit trails, smart data residency, and powerful encryption, you’re not just sharing a video; you’re building a compliant framework that protects your content, your business, and your reputation.
Common Questions About Sharing Video Privately
As post-production teams move toward more secure video sharing, the same questions tend to crop up. Getting the practical details right is what separates a clunky, insecure process from a smooth, protected workflow. Let's dig into some of the most common queries I hear.
Can People Still Download My Privately Shared Video?
This is probably the most critical question, and the answer is: it completely depends on the platform and settings you use. If you’re just using an "unlisted" link on a public video site, anyone with a simple browser extension can rip that file in seconds. You've got virtually zero control.
A real private sharing platform, on the other hand, puts you in the driver's seat. You should have the power to disable the download button for specific users or for an entire share link. This is absolutely essential for protecting your work, especially when you're sending out early cuts or sensitive material that isn't ready for wide distribution.
Being able to toggle downloads on or off for each reviewer is a core feature that distinguishes professional-grade security from just hoping for the best. Don't settle for a tool without it.
By switching off downloads, you force everyone to watch the video within the secure environment you’ve created. It dramatically cuts down the risk of unauthorized copies getting out into the wild.
What Is the Difference Between Password Protection and Viewer Login?
Both add security, but they solve different problems and offer vastly different levels of control and insight. Knowing when to use each one is key.
Password Protection: Think of this as a single key for a locked room. Anyone who has the password can get in. It's a simple, effective way to add a quick layer of security for a one-off share, like sending a cut to a vendor for a quick opinion. It's quick and dirty, but it works.
Viewer Login: This is more like a keycard system. Every single person needs their own unique credentials (like email and password or Single Sign-On) to get access. This method gives you a full audit trail, so you know exactly who watched what and when. It’s the go-to choice for ongoing projects, internal team reviews, and any workflow where accountability and compliance matter.
Basically, a password protects the content, while a user login protects the content and tracks the person.
How Do Expiring Links Work for Client Reviews?
Expiring links are a project manager’s secret weapon. They create a clear, controlled window for feedback and introduce a bit of urgency into the review cycle, which is never a bad thing. When you share video privately with an expiration date, you’re not just securing it—you’re actively managing the timeline.
Most professional platforms give you a few ways to set this up:
Set a hard date and time: Perfect for a weekend review. You can set the link to automatically deactivate at 9 AM on Monday morning.
Limit by number of views: Great for sending out screeners where you need to cap the audience size.
Set a duration after the first click: For example, the link is valid for 48 hours after the recipient first opens it.
Once that link expires, anyone clicking it gets a message saying it's no longer active. This is brilliant for preventing old, out-of-date versions from circulating and causing confusion down the line. It's a clean way to close the loop on each review round and make sure everyone is looking at the latest cut.
Question | Answer |
|---|---|
How can I stop unauthorized screen recording? | While no method is 100% foolproof, visible watermarking is the strongest deterrent. Displaying the viewer's name, email, or IP address directly on the video makes them far less likely to record their screen. |
Is my video encrypted? | Professional sharing platforms should use AES-256 encryption for both video files at rest (on their servers) and in transit (as it streams to the viewer). This is the industry standard for securing sensitive data. |
Can I restrict who sees the video based on their location? | Yes, some advanced platforms offer domain restriction or IP whitelisting. This ensures your video can only be viewed from a specific office network or a whitelisted IP address, adding a powerful layer of security for corporate or high-stakes projects. |

