New 250GB Plans LIVE now.


Your Essential Guide to DRM for Video Protection
At its heart, DRM (Digital Rights Management) for video is a lock-and-key system for your content. It’s a sophisticated set of technologies that encrypts your video files, making them unwatchable without the right "key." This system is designed to stop piracy, prevent illegal downloads, and make sure your premium content is only seen by the people who are supposed to see it.
Why DRM Is Your Digital Bouncer
Picture this: you've poured months and a small fortune into producing a flagship video series. You launch it, and within hours, you find it plastered all over illegal streaming sites for free. It’s a creator's worst nightmare and a massive financial drain that can completely devalue your hard work.
This is exactly the problem DRM solves. It acts as the digital bouncer for your valuable media, checking IDs at the door and ensuring only paying customers get in. It's the technology that makes modern streaming business models possible, from subscriptions like Netflix to pay-per-view live events and 48-hour movie rentals.
More Than Just a Lock
DRM isn't just about blocking people out; it's about enforcing the specific business rules you've set for your content. These rules are bundled into a digital "license" that a viewer's device has to get permission for before it can hit play.
This lets you control the fine print of the viewing experience:
Who gets access? Is this person an active, paying subscriber?
Where can they watch? Is this content geo-restricted to a specific country?
What devices are allowed? Can they watch on a laptop but not cast it to a big screen?
How long does access last? Is this a 48-hour rental or a permanent digital purchase?
This kind of granular control is what ensures your licensing agreements are followed to the letter and you can actually monetize your content the way you planned.
The Real Cost of Unprotected Content
Leaving your premium videos without DRM is like leaving the vault door open at a bank. The financial hit from piracy is real, and it goes beyond lost sales—it cheapens your intellectual property and your brand. The entire industry is built on the need to secure this content, and the numbers tell the story.
The global digital rights management market is exploding. It was valued at USD 4.95 billion and is on track to hit USD 13.30 billion by 2030, all thanks to the unstoppable growth of on-demand video services.
This isn't just a niche technology anymore. For any serious content owner or distributor, a solid DRM strategy is a non-negotiable part of doing business. You can learn more about these market projections and see the full analysis. Without it, you’re simply giving away your most valuable assets for free.
How a Modern Video DRM System Actually Works
A modern DRM for video system can feel a bit like a black box, but at its heart, it runs on a surprisingly simple principle: a digital lock and key. Imagine you're mailing a valuable item. You wouldn't just drop it in a postbox; you'd put it in a locked safe, and only the intended recipient would get the key to open it.
That’s exactly what DRM does for your video files. Before your content ever hits a viewer’s screen, it’s put through a precise, multi-step security process built on three core pillars: encryption, license management, and secure playback. Each step is critical, creating a solid chain of security from your servers all the way to the end user's device.
The First Pillar: Content Encryption
It all starts with encryption. This is the process of scrambling your video file so it becomes completely unreadable to anyone without authorization. We're not talking about a simple password lock here; this is a sophisticated cryptographic process. A powerful algorithm, typically AES-128, transforms your crystal-clear video into what looks like a jumbled mess of data.
Once scrambled, the video is effectively "locked." Even if a pirate manages to download the file, it’s completely useless without the specific Content Encryption Key (CEK) that was used to lock it. This first move ensures the raw video asset is secure before it even begins its journey across the internet.
The Second Pillar: License Management
Now for the gatekeeper. The license server is the brains of the whole operation. It doesn't actually store your video; its only job is to manage and hand out the "keys" (or licenses) that can unlock the encrypted content.
When a viewer hits play, their video player sends a license request to this server. The server then acts like a digital bouncer, quickly checking the viewer's credentials against the business rules you’ve set.
Is the user an active subscriber?
Are they watching from an approved country?
Have they hit their device limit?
If everything checks out, the license server generates a license containing the decryption key and sends it securely to the viewer’s device. If not, access is denied. This entire handshake happens in a split second, totally invisible to the person watching.
This infographic lays out the secure flow, showing how the content is protected by this gatekeeper before it ever reaches the viewer.
As you can see, the license server's role is absolutely critical. It validates every single playback request before giving the green light.
The Final Pillar: Secure Playback
The final piece of the puzzle clicks into place on the viewer's device. Modern browsers and devices come with a built-in security component called a Content Decryption Module (CDM). The best way to think of a CDM is as a tiny, tamper-proof safe that lives inside the device's hardware or software.
When the player gets the license from the server, it doesn't just grab the key itself. Instead, it hands the entire license off to the CDM. This module is the only part of the system that can securely access the key, use it to decrypt the video stream on the fly, and then pipe the decoded video frames directly to the screen.
By keeping the whole decryption process locked inside the CDM, the system stops malicious software or prying eyes from ever getting ahold of the decryption key or the decoded video. This hardware-level security is what makes today’s DRM so tough to beat.
This three-step dance—encryption, license management, and secure playback—is the foundation of any professional DRM setup, making sure your valuable content stays protected from start to finish.
Comparing the Three Major DRM Platforms
When you dive into the world of DRM for video, you'll quickly realize it's a landscape dominated by three giants: Google, Microsoft, and Apple. These aren't just competing technologies; they're entire ecosystems. To get your content to play everywhere your audience is, you have to get comfortable with the unique strengths and quirks of each one.
https://www.youtube.com/embed/5ZHr543MJHE
Here’s the thing: you can't just pick one. The modern streaming world demands a multi-DRM strategy to make sure your video works on every device imaginable. Tech giants like Google, Apple, and Microsoft effectively control this space, commanding over 60% of the DRM market share. They lean on their massive device and software footprints to offer protection across countless platforms. You can dig into the full DRM market analysis to see just how they maintain this grip.
Google Widevine: The De Facto Standard for Android and the Web
Google Widevine is, without a doubt, the most common DRM solution out there. Why? Because it’s baked directly into the world’s most popular operating systems and web browsers. If you need your content to play on an Android phone, in a Chrome browser, or on smart TVs from brands like Samsung and LG, then Widevine isn't just an option—it's a requirement.
Its sheer ubiquity makes it the foundation for reaching a massive global audience. A key differentiator for Widevine is its use of security levels:
Widevine L1: This is the gold standard. All the heavy lifting—content processing and decryption—happens inside a secure, hardware-based environment called a Trusted Execution Environment (TEE). Major studios mandate L1 for streaming their HD and 4K content.
Widevine L3: This is the software-based alternative. While it still offers good protection, it's considered less ironclad, so content owners often limit L3 devices to standard-definition playback.
Because of its incredible reach, Widevine is the cornerstone of almost every multi-DRM setup.
Microsoft PlayReady: The Powerhouse for Windows and Gaming Consoles
Next up is Microsoft's PlayReady, another major force in the DRM world. Its kingdom is the Windows ecosystem. It’s built right into the Microsoft Edge browser and serves as the native DRM for every Windows device, not to mention the entire Xbox gaming console family.
PlayReady is well-known for being both powerful and flexible. It gives content owners a ton of control, allowing them to define complex business rules for things like movie rentals, subscription access, and offline viewing. For a long time, it was also the DRM of choice for many smart TV makers, which gave it a solid foothold in the living room.
While Widevine has been catching up on smart TVs, PlayReady is still absolutely essential for reaching the millions of users on PCs and gaming consoles—two platforms where a huge amount of premium content is watched.
Its tight integration with all things Microsoft guarantees a secure and smooth experience for a huge, dedicated user base.
Apple FairPlay: The Gatekeeper of the Apple Ecosystem
It wouldn’t be an Apple technology if it didn’t play by its own rules. FairPlay DRM is the exclusive, non-negotiable solution for protecting video on any Apple device. That means iPhones, iPads, Macs (in Safari), and Apple TV. If your audience is on an Apple product, you have to use FairPlay.
FairPlay is woven directly into Apple's hardware and software, creating a highly secure environment that content owners trust. It's a fundamental part of Apple's native streaming protocol, HLS (HTTP Live Streaming), which makes implementation relatively simple for developers building apps for the Apple ecosystem.
The biggest "catch" with FairPlay is also its greatest strength: it's a walled garden. It works flawlessly inside its own world but doesn't play with anything outside of it. This is the clearest illustration of why a multi-DRM approach isn't just a smart move; it's a modern necessity.
A Head-to-Head Comparison
Seeing how these platforms line up side-by-side really clarifies things. Each technology serves a critical part of the market, and using them together is the only way to cover the vast majority of devices people use today.
DRM System Comparison: Widevine vs. PlayReady vs. FairPlay
Feature | Google Widevine | Microsoft PlayReady | Apple FairPlay |
|---|---|---|---|
Primary Developer | Microsoft | Apple | |
Key Platforms | Android, Chrome, Firefox, Chromecast, Smart TVs | Windows, Edge, Xbox, some Smart TVs | iOS, macOS (Safari), tvOS (Apple TV) |
Streaming Support | MPEG-DASH, HLS, CMAF | MPEG-DASH, HLS, CMAF | HLS |
Security Model | L1 (Hardware), L3 (Software) | Hardware-level and software-level protection | Tightly integrated hardware and software |
Ecosystem | Open web and Android | Windows and gaming consoles | Closed Apple ecosystem |
At the end of the day, these systems aren't really competitors. Think of them as complementary pieces of a very large puzzle. A successful DRM for video setup uses all three in harmony to give every viewer, no matter what device they're holding, secure and uninterrupted access to your content.
Integrating DRM into Your Streaming Workflow
Think of DRM for video not as a separate add-on, but as a critical thread woven directly into your video delivery pipeline. It has to work hand-in-glove with the technologies you already use for encoding, packaging, and streaming. This is where the abstract ideas of encryption and licensing meet the real-world challenge of getting a secure, high-quality stream to any screen.
At the heart of it all are modern streaming protocols. You can't just throw a giant video file over the internet and hope for the best. Instead, we break videos into small chunks and deliver them using adaptive bitrate protocols like HLS (HTTP Live Streaming) and MPEG-DASH. This is what allows a player to seamlessly switch between quality levels, giving viewers a smooth experience even on a spotty connection. DRM has to fit perfectly into this chunk-based world.
The Power of Common Encryption
Back in the day, supporting different DRM systems was a logistical nightmare. You had to create and store separate, encrypted versions of every single video file for each platform—one for Widevine, another for PlayReady, and a third for FairPlay. For anyone with a large content library, this was a massive headache for both storage and processing.
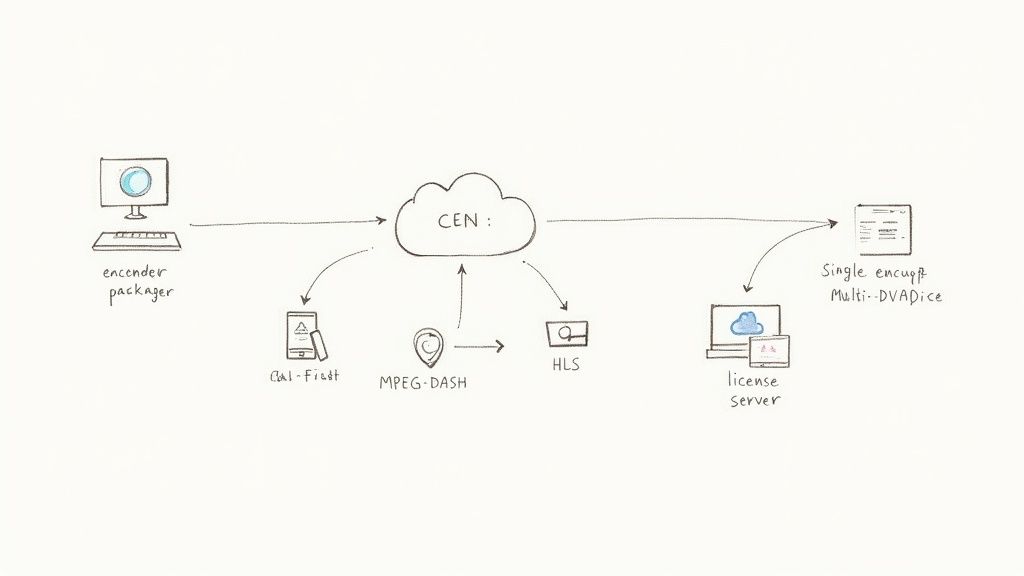
The solution to this inefficiency is a brilliant standard called Common Encryption (CENC).
CENC is a total game-changer. It lets you encrypt your video content just once. During the packaging process, the video is scrambled with a standard key, but the file’s metadata includes specific instructions for each DRM system you need to support. This "encrypt once, protect everywhere" approach is the secret sauce to a modern, efficient multi-DRM strategy.
When a device's player requests the video, it knows which DRM it uses. It simply reads the corresponding metadata to ask for the right license. The result? A single set of video files that can be securely played on almost any device, which dramatically slashes storage costs and simplifies your entire workflow.
The Practical DRM Workflow, Step by Step
So, how does this all come together in practice? Let's walk through a typical multi-DRM streaming process to see how your video is protected from start to finish.
Encoding and Packaging: First, your source video is encoded into several different quality levels (like 480p, 720p, and 1080p). Then, during the packaging stage, it's encrypted using CENC and chopped into small segments for HLS or DASH delivery. The packaging tool also embeds the specific metadata each DRM system will need.
Player Initialization: When a viewer hits play, their video player first downloads the stream manifest file. This file acts like a table of contents, telling the player about all the available quality levels and, most importantly, signaling that the content is encrypted.
License Request: The player, following instructions in the manifest, talks to the device's native Content Decryption Module (CDM). The CDM creates a license request, which the player sends off to your DRM license server.
License Server Validation: The license server gets the request and immediately authenticates it based on your business rules. Is the user a paying subscriber? Are they watching from an approved country? Have they hit their device limit?
Secure Playback: If everything checks out, the license server grants a license containing the decryption key. The player hands this license to the CDM, which securely decrypts the video chunks just milliseconds before they appear on the screen. The result is seamless, protected playback.
This entire handshake—from the play button click to the video appearing—happens in the blink of an eye. A well-designed DRM system is completely invisible to the viewer, providing rock-solid security without getting in the way of the experience.
This seamless integration is non-negotiable today. With more people watching on more devices than ever, the demand for secure delivery is exploding. The VOD segment alone is projected to grow at a CAGR of 19.8%, fueled by viewers on every screen imaginable.
For media teams, a smooth DRM workflow isn't just a technical detail—it's a core business requirement. And for those looking to sharpen their production pipelines, understanding these integrations is essential. It’s a key part of the modern editor’s toolkit, which is a central focus for platforms like PlayPause that help creative teams streamline their entire review and approval process.
Choosing Your DRM Implementation Strategy
So, you understand the moving parts of DRM for video. Now for the big question: how do you actually implement it? This is a major fork in the road, forcing you to choose between two very different paths. You can either build a DRM system from the ground up or partner with a specialized DRM-as-a-Service (DRMaaS) provider.
Each option has huge technical, financial, and operational consequences. The right call really boils down to your team’s in-house skills, budget, and what you’re trying to achieve in the long run.
The Self-Hosted DRM Path
Let's be blunt: building a DRM solution yourself is a monumental task. It’s not just a matter of spinning up a server. You’re effectively signing up to become a security expert, a high-availability infrastructure manager, and a compliance specialist who can navigate the labyrinthine licensing rules from Google, Microsoft, and Apple.
Going this route demands a dedicated team of engineers who are deeply skilled in:
High-Availability Infrastructure: Your license servers can't go down. Period. Any downtime means viewers can't watch your videos, which directly hits your revenue and tanks customer trust.
Security and Compliance: The major DRM providers constantly issue updates and enforce strict security rules. If you fall behind on patching vulnerabilities or meeting new requirements, your content might simply stop playing on certain devices.
Complex Integrations: You’d be responsible for building and maintaining all the connections between your encoders, video players, and the DRM systems themselves. Each one has its own API and quirks.
For most companies, the overwhelming cost and complexity just don't add up. It’s a massive distraction from what should be your main focus: creating and delivering amazing content.
The DRM-as-a-Service (DRMaaS) Model
This brings us to the far more common and practical approach: working with a DRMaaS provider. These are companies that have already done all the heavy lifting. They’ve built the robust, scalable, and secure infrastructure needed to handle the entire DRM licensing process for you. Instead of starting from scratch, you just plug their service into your video workflow using an API.
Think of it like electricity. You could build your own power plant to keep the lights on, but it's infinitely easier and more reliable to just plug into the grid. A DRMaaS provider is the power grid for your content protection.
This model is the default choice for the vast majority of streaming services, broadcasters, and media companies for a few very good reasons.
Why a DRMaaS Partner Makes Sense
Partnering with a DRMaaS provider lets you offload the entire technical headache of content protection. This frees up your team to focus on what they do best. The benefits are clear, immediate, and can dramatically simplify your operations while lowering your risk.
Here’s what you get right out of the gate with a solid DRMaaS solution:
Multi-DRM Support Out of the Box: Get instant access to Widevine, PlayReady, and FairPlay through a single, unified API. Just like that, your content is ready for virtually every major device and browser.
Expert Support: You’re not just buying software; you’re gaining a team of specialists who live and breathe DRM. They’re the ones handling security updates, compliance audits, and troubleshooting.
Faster Time-to-Market: Forget spending months—or even years—on development. You can integrate a proven DRM solution in a fraction of the time and launch your secure service much, much faster.
Scalability and Reliability: DRMaaS platforms are engineered to handle huge traffic spikes, like the ones you see during a major live event, without even breaking a sweat.
Cost-Effectiveness: You skip the massive upfront investment and ongoing operational costs of building and maintaining your own system. Pricing is usually based on usage, so it scales right alongside your business.
Choosing the right partner is crucial for your long-term success. If you're figuring out how a DRMaaS provider can fit into your workflow and need some expert guidance on the integration process, our team is here to help. Feel free to get in touch with PlayPause to talk through your specific security needs.
Layering Your Defenses Beyond Encryption
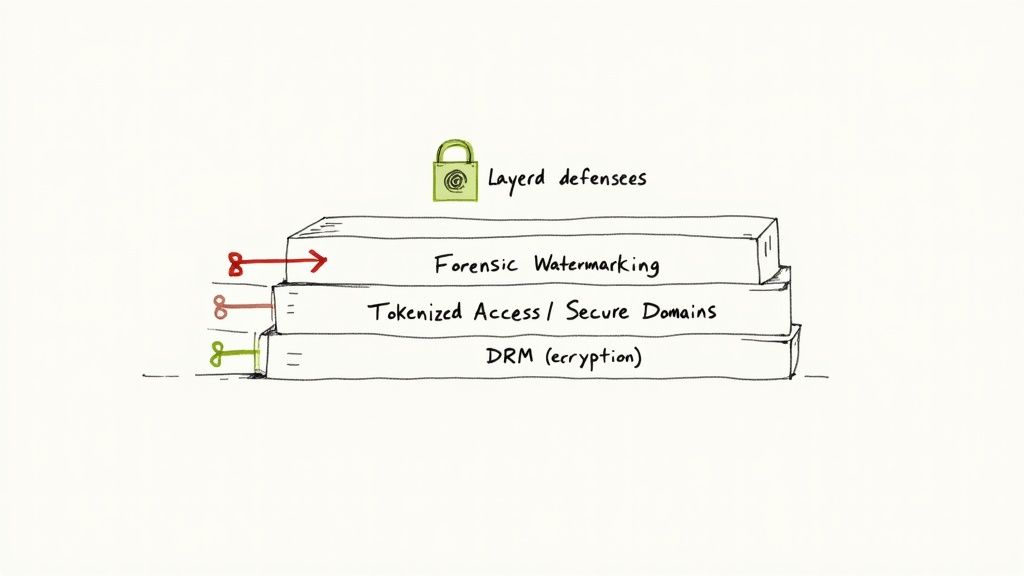
A solid DRM for video strategy is your first line of defense, but it's not a silver bullet. Think of DRM as a high-tech lock on your digital front door. It’s fantastic at keeping unauthorized people from walking in and playing your video. But what about an authorized user who decides to record their screen?
That’s where thinking in layers comes in. True content protection means adding other technologies on top of DRM to tackle different kinds of piracy. By combining encryption with other security tools, you build a much tougher system that can stand up to more creative threats.
Pinpointing Leaks with Forensic Watermarking
The one big thing standard DRM can't stop is an authorized user sharing the content. This is exactly the problem forensic watermarking was designed to solve. We’re not talking about a visible logo in the corner of the screen; a forensic watermark is a completely invisible identifier embedded into every single video stream.
This unique identifier is imperceptible to the viewer, but it’s permanently tied to their user account or even that specific viewing session. If a watermarked video ever pops up on a pirate site, you can analyze the file, pull out that hidden code, and trace it straight back to the account that leaked it. It’s a digital fingerprint.
The real power here is deterrence. When users know that any pirated copy can be traced directly back to them, the personal risk of sharing content skyrockets. It stops piracy before it even starts.
This technology is absolutely essential for protecting pre-release content, like early movie screeners or sensitive internal videos, where finding the source of a leak is non-negotiable.
Strengthening Access with Tokenization
Another critical layer is tokenized access. Instead of just verifying a user has a valid subscription, this method uses a dynamic, short-lived security token for every single playback request. Each time someone hits "play," your system generates a unique, one-time-use token that gives them permission for that session and that session only.
This approach tightens security in a few key ways:
Stops Session Hijacking: Stolen login details or session cookies become far less valuable to a hacker because a fresh, unique token is required for every new playback.
Enforces Concurrency Rules: It makes it much harder for people to share their login credentials, because you can precisely control how many active streams are allowed per account at any given time.
Adds Time Limits: Tokens can be set to expire quickly, meaning access rights are constantly being re-checked and old, forgotten links can't be exploited.
When you combine strong DRM encryption with forensic watermarking and tokenized access, you graduate from simply blocking playback. You build a complete security system that not only locks down your content but also gives you the tools to deter, trace, and shut down leaks for good.
Common Questions About DRM for Video
Diving into DRM for video can feel a bit daunting. People often have very practical questions about how it all works in the real world. Let's tackle some of the most common ones I hear from teams trying to get a handle on it.
Does DRM Harm the User Experience?
This is probably the biggest concern, and for good reason. In the past, DRM could be clunky and intrusive. Thankfully, those days are long gone.
When set up correctly, modern DRM is completely invisible to your audience. The whole process—the player asking for a key, the server checking permissions, and the key being sent back—happens in a flash, completely behind the scenes. Your authorized viewers get a smooth, instant playback experience, just as if the content wasn't protected at all.
Is DRM Completely Unbreakable?
Let's be realistic: no security system is 100% foolproof. The real goal of DRM isn't to create an unbreakable vault, but to make piracy so difficult, expensive, and time-consuming that it's just not worth the effort for most people.
Hardware-level protection, like Widevine L1 or Apple FairPlay, gets as close to "unbreakable" as you can get. Because it's baked directly into the device's hardware, it creates a secure fortress that stops casual piracy dead in its tracks.
A well-implemented DRM strategy effectively neutralizes the 99% of piracy threats that do the most economic harm. You're not aiming for theoretical perfection; you're aiming for practical, real-world protection.
How Much Does Video DRM Cost?
The cost really depends on how you go about it. Trying to build a DRM system from the ground up is a massive technical and financial commitment. The upfront investment and ongoing maintenance costs are just too high for most companies.
That's where DRM-as-a-Service (DRMaaS) providers come in. They make professional-grade security accessible and affordable, typically with a pricing model that grows with you.
Pay-as-you-go: You're usually billed based on the number of license requests your videos generate each month.
Scalable: This means you don't need a huge upfront budget. Your costs naturally scale as your viewership increases.
This model has made top-tier content protection a viable option for everyone, from independent creators to large enterprises. If you want to dig deeper into different content protection strategies, you can find more discussions over on the PlayPause blog.

